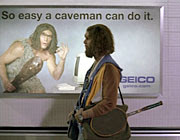
Be the Caveman
 I just read a great story by InformationWeek's Sharon Gaudin titled Interview With A Convicted Hacker: Robert Moore Tells How He Broke Into Routers And Stole VoIP Services:
I just read a great story by InformationWeek's Sharon Gaudin titled Interview With A Convicted Hacker: Robert Moore Tells How He Broke Into Routers And Stole VoIP Services:Convicted hacker Robert Moore, who is set to go to federal prison this week, says breaking into 15 telecommunications companies and hundreds of businesses worldwide was incredibly easy because simple IT mistakes left gaping technical holes.
Moore, 23, of Spokane, Wash., pleaded guilty to conspiracy to commit computer fraud and is slated to begin his two-year sentence on Thursday for his part in a scheme to steal voice over IP services and sell them through a separate company. While prosecutors call co-conspirator Edwin Pena the mastermind of the operation, Moore acted as the hacker, admittedly scanning and breaking into telecom companies and other corporations around the world.
"It's so easy. It's so easy a caveman can do it," Moore told InformationWeek, laughing. "When you've got that many computers at your fingertips, you'd be surprised how many are insecure." (emphasis added)
So easy a caveman can do it? Just what happened here?
The government identified more than 15 VoIP service providers that were hacked into, adding that Moore scanned more than 6 million computers just between June and October of 2005. AT&T reported to the court that Moore ran 6 million scans on its network alone...
Moore said what made the hacking job so easy was that 70% of all the companies he scanned were insecure, and 45% to 50% of VoIP providers were insecure. The biggest insecurity? Default passwords.
"I'd say 85% of them were misconfigured routers. They had the default passwords on them," said Moore. "You would not believe the number of routers that had 'admin' or 'Cisco0' as passwords on them. We could get full access to a Cisco box with enabled access so you can do whatever you want to the box...
He explained that he would first scan the network looking mainly for the Cisco and Quintum boxes. If he found them, he would then scan to see what models they were and then he would scan again, this time for vulnerabilities, like default passwords or unpatched bugs in old Cisco IOS boxes. If he didn't find default passwords or easily exploitable bugs, he'd run brute-force or dictionary attacks to try to break the passwords.
So, we have massively widespread scanning, discovery of routers, and attempted logins. No kidding this is caveman-fu.
And Moore didn't just focus on telecoms. He said he scanned "anybody" -- businesses, agencies and individual users. "I know I scanned a lot of people," he said. "Schools. People. Companies. Anybody. I probably hit millions of normal [users], too."
Moore said it would have been easy for IT and security managers to detect him in their companies' systems ... if they'd been looking. The problem was that, generally, no one was paying attention.
"If they were just monitoring their boxes and keeping logs, they could easily have seen us logged in there," he said, adding that IT could have run its own scans, checking to see logged-in users. "If they had an intrusion detection system set up, they could have easily seen that these weren't their calls." (emphasis added)
Didn't someone tell Robert Moore that "IDS is dead?" Apparently all of these victim companies heard it, and turned off their visibility mechanisms.
My advice? Be the caveman. Perform adversary simulation. This is the simplest possible way to pretend you are a bad guy and get realistic, actionable results.
- Identify all of your external IP addresses.
- Scan them.
- Try to log into remote administration services you find in Step 2.
- Report your findings to device owners when you gain access.
How difficult is that? This methodology is nowhere near to being effective against targeted threats who want to compromise you specifically, but they would work against this opportunistic threat.
PS: If I hear one more time that "scanning is too dangerous for our network" I will officially Lose It. Scanning of external systems happens 24x7. If you really don't want an authorized party to scan your external network, try setting up a passive detection systems like PADS and wait for a bad guy to ignore the fragility of your systems and scan them for you. Gather his results passively and then act on them.



Comments
Doesn't that continue to promote the negative stereotype that cavemen are dumb... I mean they did discover fire for us. For shame ;)
One admin asked me to halt the scans because it was causing his Brocade switches to lock up. I gave him 2 weeks to test and deploy software updates. I then reminded him that just because it's "internal" does not mean its safe.
hahaha, Me and you both. I said the same thing in my post on PCI requirements. If a tool you've downloaded has been tested on a lab network and audited for backdoors, there should be no qualms about scanning prod systems. ;)
I hate hearing the words “We don’t scan against production.” Frankly, I don’t care to either. There’s just something annoying about, “If you bring down production with your tests, you’re dead meat/fired/a goner.” Well, if your production environment was built properly, you shouldn’t have this problem. People who say this are likely responsible for the most delicate, insecure network or system around. Seriously. -- More on ambiguous security standards
Also, anyone who says "this attack could never bring down a machine" or "the web server gets hit with this stuff all the time" hasn't been involved with an enterprise scanning operation for long. As Joe mentioned above, there are all kinds of side effects that you'd never expect. I've seen "run of the mill" scanning activity take down an external server against everyone's expectations due to very minor differences in the type of check that the vendor had provided us with (vs. that which was circulating in the wild).
At the end of the day, it doesn't matter how "delicate" or "insecure" a security geek thinks the networks is--it's the job of the security professional to remediate vulnerabilities while maintaining network availability, and any security professional who would rather score points by taking out their own network probably shouldn't be employed for long.
>anyone who says "this attack could never bring down a machine" or
>"the web server gets hit with this stuff all the time" hasn't been
>involved with an enterprise scanning operation for long.
ummmm - have you read Richards stuff much? I suspect he's been at least a little involved with enterprise scanning for at least a little while