Welcome to Network Security Monitoring in the Cloud
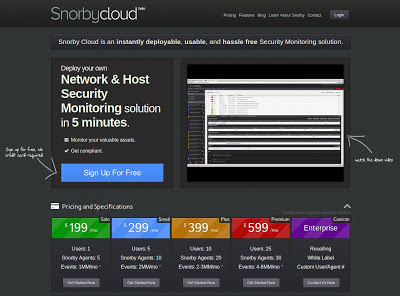
I just watched an incredible technical video. If you have about 10 minutes to spare, and want to be amazed, take a look at Snorby Cloud.
I think the video and Web site does an excellent job explaining this new offering, but let me provide a little background.
Many of the readers of this blog are security pros. You're out there trying to defend your organization, not necessarily design, build, and run infrastructure. You still need tools and workflows that accelerate your incident detection and response process though. So, you work as a security admin, system admin, storage admin, database admin... you get the picture. You manage to keep up, but you probably wish you could focus on finding bad guys, as quickly as possible, without taking care of all the *stuff* that you need to do your job.
While many of you are security experts, some are just beginning your journeys. The responsibilities of being an admin of four or more different shades is overwhelming. Furthermore, you don't have the experience, or budget, or support to get the security data and escalation paths needed to defend your network. How can you improve your skills when you're constantly overwhelmed?
Both kinds of users -- senior and junior alike -- are going to find something intriguing about Snorby Cloud. Maybe you've heard of Snorby before, as a Web-based interface to Network Security Monitoring data. Doug Burks packages it with Security Onion (SO), and you can try it via live CD or .iso in a VM. It looks great on my iPad! There's even a mobile version on iTunes.
Snorby Cloud would be cool if it just put the Snorby Web application in the cloud, and managed the administrative side of security infrastructure for you. For example, you'd log into the cloud interface and be greeted by the graphs you remember from traditional Snorby.
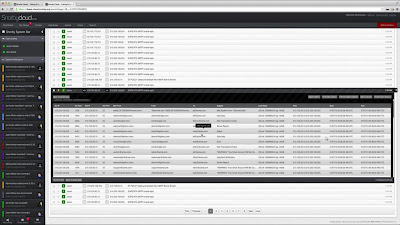
However, you have to think of this as a new, better version of Snorby, collecting far more useful data, and making it rapidly available to the analyst. For example, the following shows SMTP logs available in the interface:
You can just as easily access host-based logs for the same victim computer:
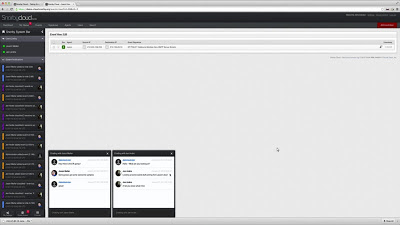
As you investigate the incident, you can see who else on your team is working and what they did. You can also chat with them in real time.
I could say a lot more about this new tool, but I think watching the video will convey some of what it can do. My next step is to get the agents running on a test network so I can drive the console myself and become more familiar with it.
Snorby Cloud is a product from Packet Stash. Follow them at @packetstash for updates.
Disclaimer: I'm friends with this team; I hired two of the co-founders into GE-CIRT, and later worked with all three co-founders at Mandiant.





Comments